WeTheNorth Market Access Guide —
Tor & Security Setup
This complete guide covers everything you need to securely access WeTheNorth in 2026: Tor Browser installation, Tails OS setup, PGP key generation, Bitcoin and Monero wallet configuration, and step-by-step marketplace login instructions. Follow each section to establish a full operational security baseline before connecting to the official onion address.
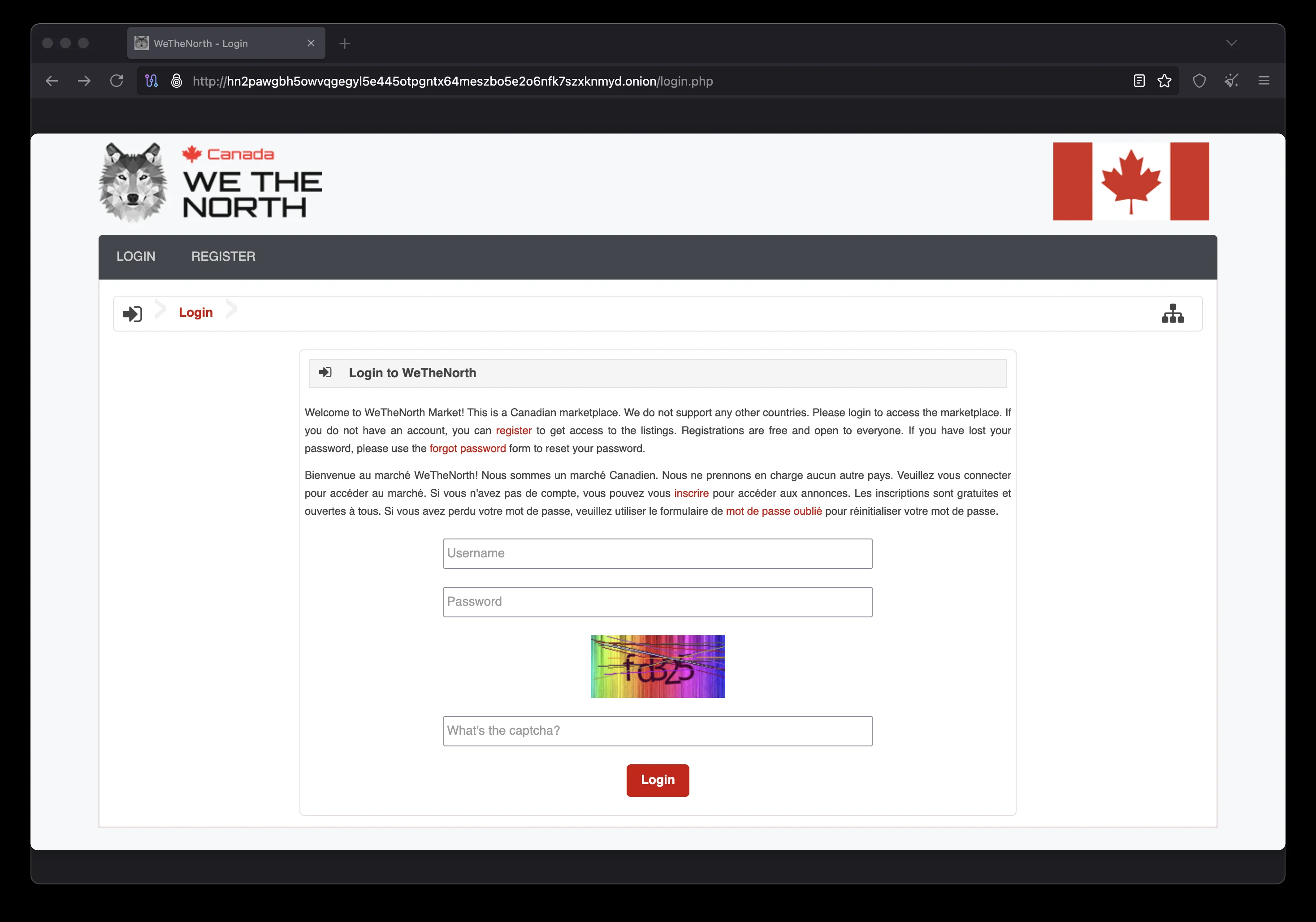
the platform secure login — accessed via Tor Browser with anti-phishing phrase and PGP 2FA
Step 1 — Download & Configure Tor Browser
Tor Browser is the mandatory tool for accessing WeTheNorth Market. It routes all traffic through the Tor network and is the only browser that can resolve .onion addresses.
Downloading Tor Browser Safely
Visit the official Tor Project download page and select Tor Browser for your operating system: Windows, macOS, or Linux. The Tor Project is a 501(c)(3) non-profit organization; all software is free and open-source. Do not download Tor Browser from any other source — mirrors and third-party distributions may contain malware.
After downloading, verify the package signature using the PGP key published at torproject.org/dist. The Tor Project signs every release with their GPG key. Verification confirms the download was not tampered with in transit — an important step for the platform Market users in adversarial network environments.
Setting the Security Level
After launching Tor Browser, click the shield icon in the toolbar. Select Change and set security to Safest. This setting disables JavaScript globally, blocks web fonts, restricts HTML5 media, and limits dangerous browser APIs. The marketplace is designed to operate fully at the Safest security level — you do not need to downgrade security to access it.
Privacy Guides maintains an excellent Tor overview guide with additional configuration tips. For WTN users, the EFF's Surveillance Self-Defense project provides context on threat modeling that shapes how to configure Tor for marketplace use.
Never Use Regular Browsers for the market
Chrome, Firefox, Safari, and Edge cannot connect to .onion addresses and do not provide Tor anonymity. Using Tor-to-web proxies (like Tor2Web) for the platform access exposes your real IP address to the proxy operator. Always use Tor Browser directly.
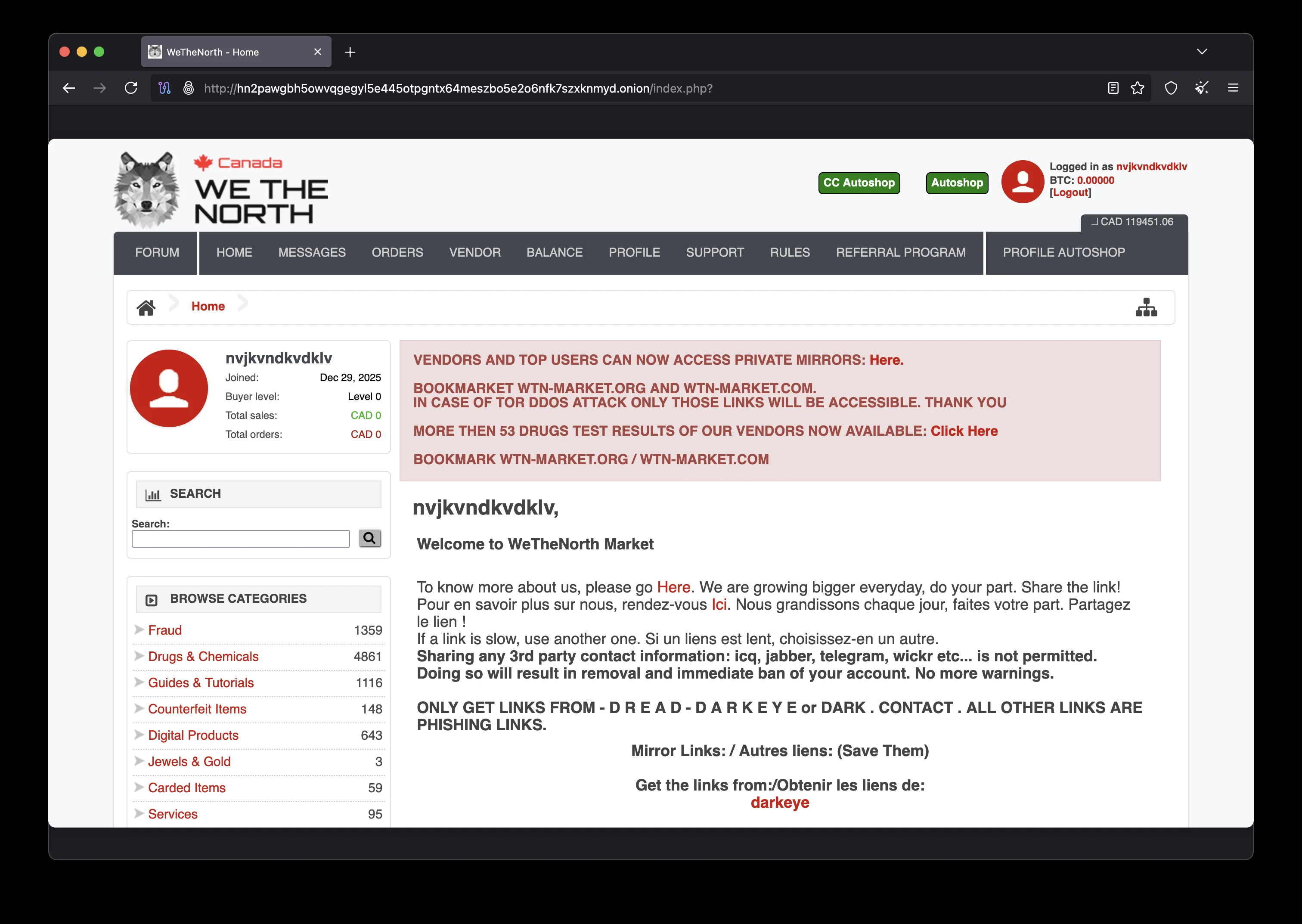
the platform homepage as seen in Tor Browser at Safest security level — no JavaScript required
Step 2 — Install Tails OS for Maximum Security
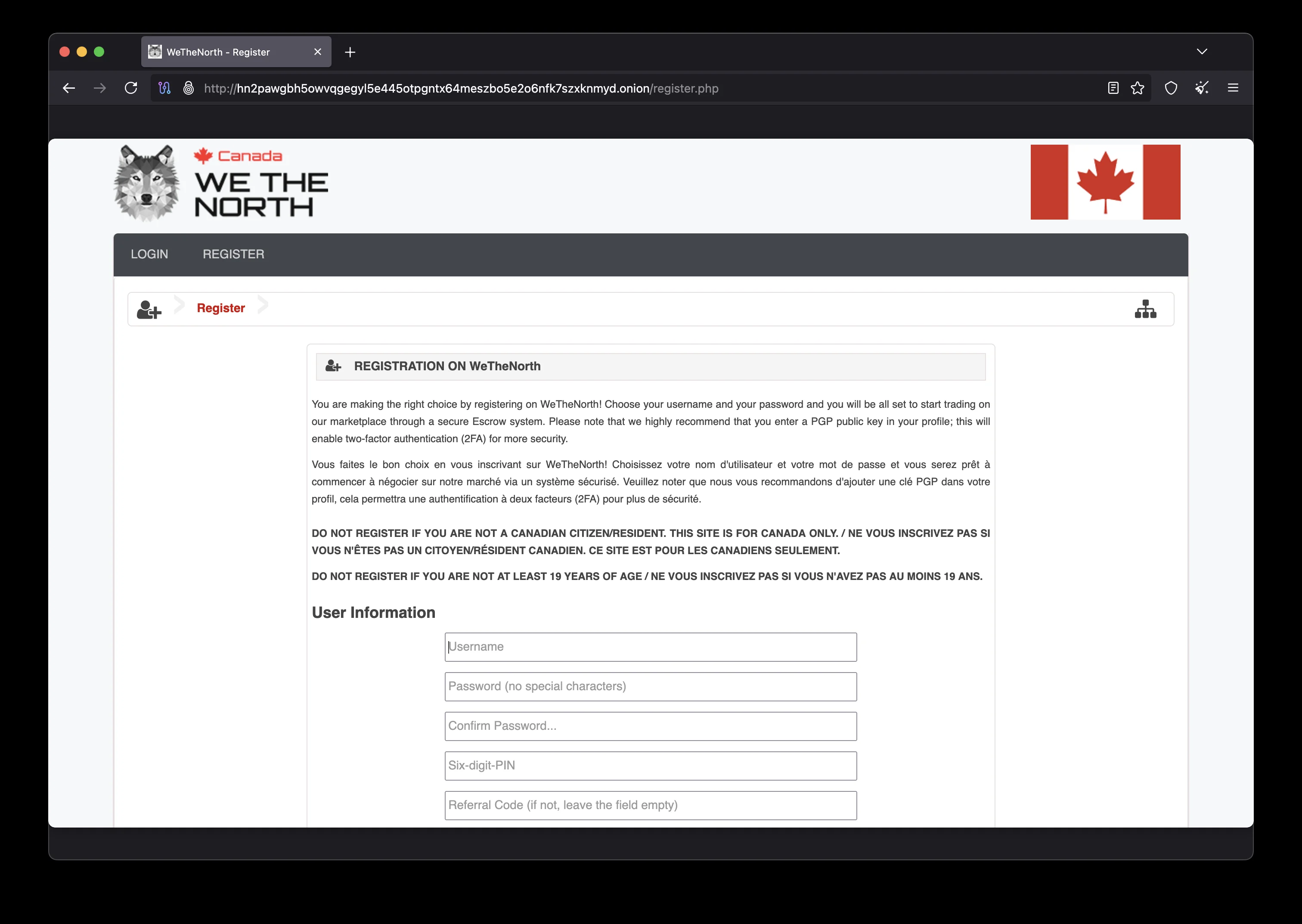
WTN registration from Tails OS — no email required, pseudonymous account creation
Tails OS (The Amnesic Incognito Live System) is the most secure environment for accessing WeTheNorth Market. Tails boots from a USB drive, routes every network connection through Tor automatically, and stores nothing on the host computer after shutdown. It is the operating system used by journalists, activists, and security researchers facing surveillance threats — and the gold standard for anonymous darknet market access.
Download the Tails OS image from tails.boum.org/install and verify the download using their included verification tools. Create a bootable USB using Balena Etcher or the Tails installer. Configure UEFI/BIOS to boot from USB. On first boot, Tails walks you through the Welcome Screen where you can configure an Administration password and choose a persistent storage volume (encrypted with Luks) for saving marketplace settings, PGP keys, and cryptocurrency wallets.
Alternatives: Whonix and Qubes OS
If you prefer a desktop environment, Whonix provides Tor-routed networking via a two-VM Gateway/Workstation architecture. Install Whonix in VirtualBox or KVM on your existing OS. All the marketplace sessions run inside the isolated Whonix Workstation VM while all traffic transits through the Whonix Gateway. For maximum compartmentalization, Qubes OS runs multiple isolated VMs (qubes) and natively integrates Whonix for Tor-based browsing. Qubes is the most secure desktop OS available for WTN users managing multiple security domains simultaneously.
Step 3 — Generate PGP Keys for WeTheNorth 2FA
PGP two-factor authentication is WeTheNorth's most powerful account protection. This section covers key generation, export, and upload to your WTN account.
The OpenPGP standard, documented at openpgp.org, is a cryptographic framework for encrypting messages, signing files, and verifying identity. The marketplace implements PGP 2FA by sending you an encrypted challenge at login that only your private key can decrypt.
Generating Your WTN PGP Key
Install GnuPG (pre-installed in Tails OS). Open a terminal and run:
gpg --full-generate-key
Select these options:
- Key type: RSA and RSA (option 1)
- Key size: 4096 bits (maximum)
- Expiry: 0 (does not expire)
- Real name: use a pseudonym, never your real name
- Email: optional, can be blank or pseudonymous
- Passphrase: strong, unique, stored in KeePassXC
Exporting Your Public Key
Export your public key to paste into the platform account settings:
gpg --armor --export YOUR_KEY_ID
In your account settings, navigate to Security → PGP 2FA. Paste your public key and save. Enable two-factor authentication. On each subsequent WTN login, the platform sends a PGP-encrypted block. Copy it, decrypt with:
gpg --decrypt
Paste the decrypted code back into the 2FA field to complete login. Store your private key and passphrase in KeePassXC and back up to an encrypted VeraCrypt container on a dedicated USB drive stored offline.
the marketplace PGP 2FA and anti-phishing setup in account security settings
Step 4 — Set Up BTC & XMR Wallets for WeTheNorth
Monero (XMR) Wallet Setup
Monero is the preferred payment method due to its built-in transaction privacy. Download the official Monero GUI wallet or the lighter Feather Wallet from getmonero.org/downloads. Create a new wallet and immediately write your 25-word seed phrase on paper — store it in a waterproof location away from the computer.
Configure your Monero wallet to connect through Tor by selecting a remote node accessible via a .onion address, or run your own Monero node for maximum privacy. The Monero node hides your wallet transactions from the remote node operator. Fund your XMR wallet through a non-KYC exchange or a peer-to-peer service for the strongest privacy chain from fiat to marketplace deposit.
Bitcoin (BTC) Wallet Setup
For Bitcoin, use Electrum Wallet (available at bitcoin.org) or Sparrow Wallet, both configured to connect through your own Bitcoin node or Tor-accessible Electrum servers. When using BTC on the marketplace, consider running your deposit through a CoinJoin session (e.g., Whirlpool in Sparrow) before depositing to your account. This breaks the transaction graph and severs the link between your on-chain identity and the marketplace account.
Seed Phrase Security
Never store your Monero or Bitcoin seed phrase digitally. Write it on paper or stamp it in steel. Store in a separate location from the device used to access the platform. Encrypt digital backups with VeraCrypt.
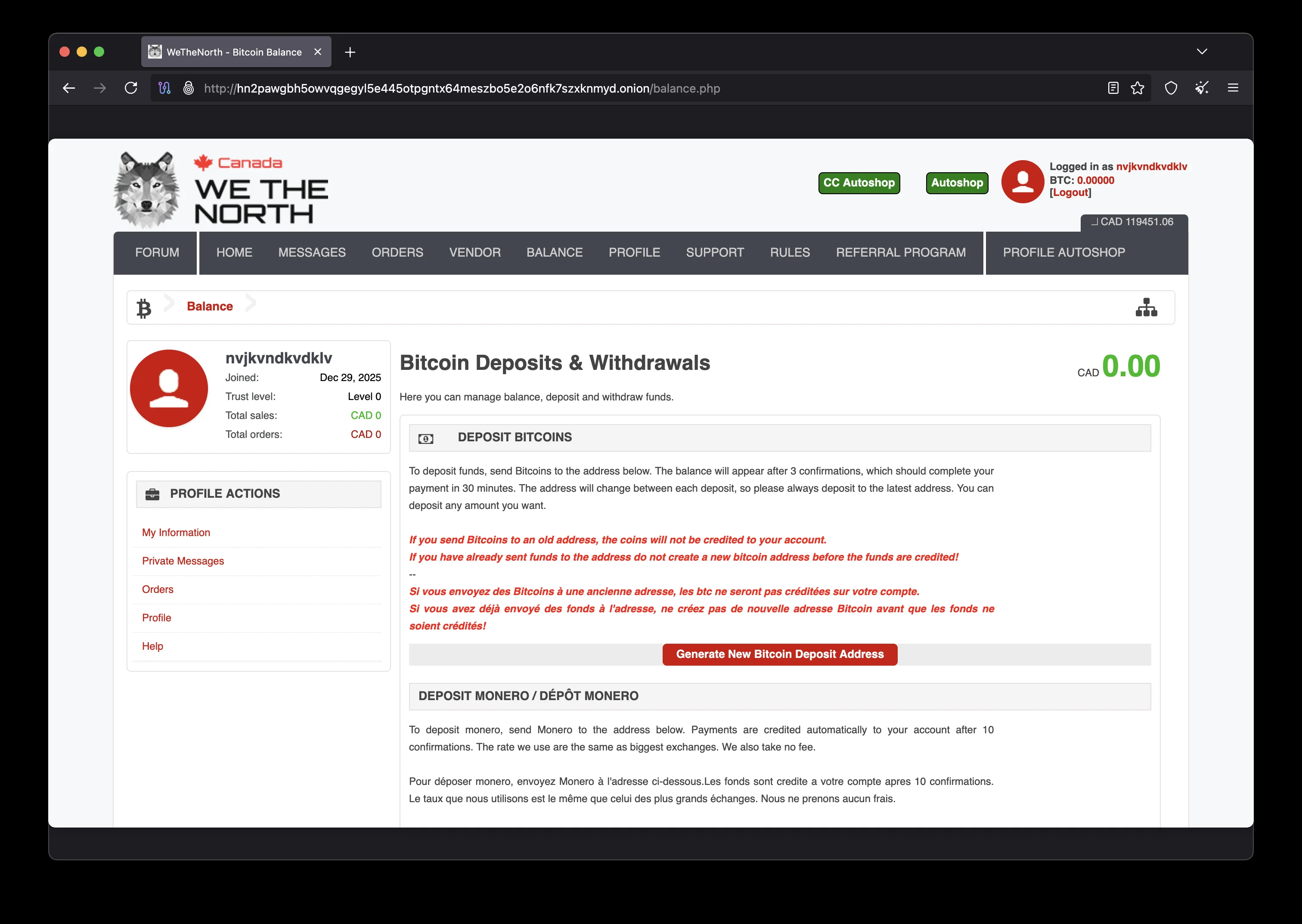
WTN deposit interface — BTC and XMR addresses with block confirmation requirements
the platform wallet — confirmed BTC and XMR balances available for escrow-protected purchases
Step 5 — Accessing WeTheNorth Market via Tor
With Tor Browser installed (ideally from within Tails OS), your PGP key generated, and your cryptocurrency wallet funded, you are ready to access the marketplace. The official WTN onion address is:
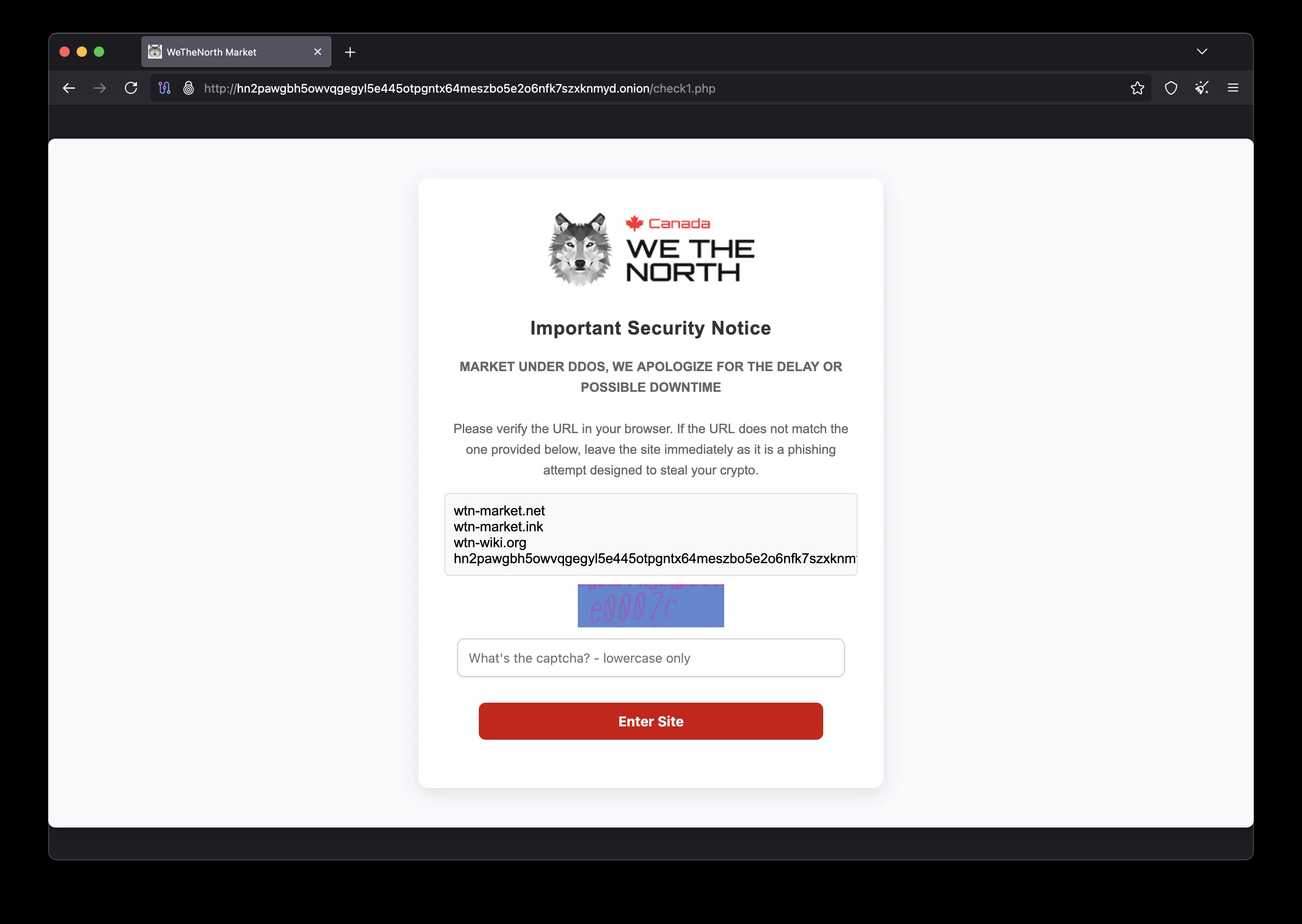
Paste this URL into Tor Browser's address bar and press Enter. The first connection to the platform may take 5–15 seconds as Tor establishes the onion circuit. On the the platform login page, before entering any credentials:
- Confirm your personal anti-phishing phrase is displayed correctly
- Verify the .onion URL matches exactly — no extra characters
- Ensure Tor Browser's connection indicator shows a secure Tor circuit
- Enter your WeTheNorth username and password
- Complete PGP 2FA challenge if enabled (strongly recommended)
For first-time WeTheNorth registration, click the Register link. You need only a username and password — no email address required. Upload your PGP public key during registration and set your personal anti-phishing phrase immediately. These two actions should be done before placing any orders or depositing cryptocurrency.
All verified mirror links are published at mirrors.wethenorthdnm.world. If the primary onion address is unreachable, try alternate mirrors — all are PGP-signed and hosted on the same WTN infrastructure. The official WeTheNorth information site and wethenorthdnm.world main page are also authoritative sources for verified WTN onion addresses.

WeTheNorth Market escrow confirmation — BTC and XMR held securely until buyer confirms delivery
Step 6 — Advanced Security for WeTheNorth Users

Advanced operational security for the marketplace — OPSEC practices for Canadian users
Operational Security (OPSEC) for WTN
Beyond technical tools, operational security (OPSEC) is critical for all marketplace users. OPSEC is the practice of protecting identifying information in day-to-day operations. Key OPSEC principles:
- Never discuss marketplace activity on clearnet platforms (Reddit, Discord, Telegram)
- Use a unique pseudonymous username not used on any other platform
- Never combine marketplace sessions with clearnet browsing in the same Tor instance
- Do not log in to the marketplace from work, school, or library networks
- Shut down Tails OS completely after every marketplace session — do not hibernate
- Keep all marketplace login credentials offline in KeePassXC only
Secure Communication on WeTheNorth
All vendor-to-buyer messaging on WeTheNorth Market should use PGP encryption for sensitive information (delivery addresses, special instructions). Never send unencrypted personal information over any darknet marketplace messaging system. Learn PGP encryption best practices at openpgp.org. For file sharing with vendors, use OnionShare to transfer files over Tor without clearnet exposure.
The Wikipedia article on operational security provides an excellent overview of OPSEC principles originally developed for military use but now essential for anyone conducting sensitive online activities, including WTN transactions.
Privacy Technology Behind Secure WeTheNorth Access
Understanding the privacy technologies used to protect your WTN sessions helps you make informed security decisions and recognize when your protection may be insufficient.
How Tor Protects Your WeTheNorth Connection
When you connect to the marketplace onion address through Tor Browser, your traffic is encrypted in three layers and routed through at least three volunteer relay nodes selected from thousands of Tor relays worldwide. The guard (entry) relay knows your real IP address but not your destination. The middle relay knows neither your IP nor the destination. The exit relay — when connecting to regular websites — knows the destination but not your IP. When accessing WeTheNorth's onion address, there is no exit relay at all: the connection terminates within the Tor network at the onion service, providing the highest level of Tor anonymity available.
This architecture means that no single entity in the network path — not your ISP, not the Tor relay operators, not the marketplace server — can connect your real identity to your marketplace activity. The marketplace operators cannot see your IP address; your ISP cannot see that you are accessing it; the relay operators see only encrypted traffic passing through. This is the fundamental security guarantee that makes the Tor network the correct tool for accessing the WTN marketplace.
Monero vs. Bitcoin: Privacy Comparison for WTN
The choice between Monero and Bitcoin for WTN transactions has significant privacy implications. Bitcoin operates on a transparent public blockchain: every transaction is permanently recorded and publicly visible. Sophisticated blockchain analytics firms — including Chainalysis, Elliptic, and CipherTrace — specialize in tracing Bitcoin transaction graphs to identify real-world actors behind addresses. Law enforcement agencies use these tools routinely in darknet market investigations.
Monero, by contrast, uses cryptographic techniques that make transaction tracing practically infeasible. Ring signatures blend your transaction with multiple decoy outputs, making it impossible for outside observers to determine which input is the real one. Stealth addresses ensure that the recipient's address is never recorded on the blockchain in a form linkable to their public address. RingCT hides transaction amounts completely. These three features together mean that Monero transactions leave no analyzable trail on the blockchain — a fundamental design difference from Bitcoin.
For WTN users, this means that XMR deposits and withdrawals cannot be linked to your on-chain cryptocurrency history by any third party. If you acquire XMR through a privacy-preserving method and use it on WeTheNorth, the financial trail ends at your wallet. Bitcoin can achieve higher privacy through CoinJoin mixing, but requires additional steps and tools, and mixed Bitcoin is increasingly flagged by centralized exchanges. For most WTN users, Monero is the recommended payment method. Download the official Monero wallet from getmonero.org and never from third-party sources.
PGP Encryption: Why It Matters for WTN Communications
PGP (Pretty Good Privacy), standardized as OpenPGP and documented at openpgp.org, uses asymmetric cryptography with a public key (shareable) and private key (secret). Anyone can encrypt a message to you using your public key, but only your private key can decrypt it. On WeTheNorth Market, PGP serves two critical functions:
- PGP 2FA: WeTheNorth sends you a PGP-encrypted login challenge. You must decrypt it to prove possession of your private key, even if an attacker has your password.
- Message encryption: Encrypt delivery addresses and sensitive information sent to vendors. Even if the market's messaging system were compromised, encrypted messages remain unreadable without your private key.
GnuPG, the open-source implementation of OpenPGP available at gnupg.org, is the standard tool for PGP on all platforms. It is pre-installed in Tails OS. Your private key should never leave your secure device and should be protected by a strong passphrase stored in KeePassXC. Back up the private key to an encrypted VeraCrypt container on a separate USB drive kept offline.
Additional Security Tools for WeTheNorth Users
Beyond the core tools covered in this guide, WTN users managing significant volumes of activity benefit from additional privacy-enhancing technologies. OnionShare enables secure file transfers over Tor between buyers and vendors without clearnet exposure. The EFF's guide to Tor and HTTPS explains how encryption layers interact. For users who need to securely communicate outside WeTheNorth's built-in messaging, Signal (for mobile) or Briar (for Tor-native messaging) are recommended alternatives. Never use unencrypted SMS, WhatsApp, or standard email to discuss WeTheNorth Market transactions — these communication channels are accessible to law enforcement with standard legal process.
Finally, regularly check the WeTheNorth mirrors page for any security announcements, PGP key updates, or onion address changes published by the WTN administration. Following official WeTheNorth channels ensures you have current verified links and are not operating on outdated information that could expose you to phishing risk.
WeTheNorth Platform Security Reference
Before accessing the WeTheNorth marketplace, understanding its core features helps buyers and sellers use it safely and effectively. The platform operates as an anonymous hidden service on the Tor network — accessible only through .onion addresses.
Anonymous & Protected Access
The marketplace is designed for fully anonymous access. No email address, phone number, or real identity is required to register. All connections route through Tor's hidden service infrastructure, meaning neither the marketplace operators nor any network observer can link your browsing activity to your real identity. The platform's anonymous architecture, combined with PGP 2FA, creates a protected environment for buyers and sellers operating within Canada. For a trusted, legitimate marketplace experience, always verify the onion URL and your anti-phishing phrase before logging in. New users should read our WeTheNorth onion access home page to verify the current official onion address.
Multisig Escrow & Seller Protection
Beyond standard escrow, the marketplace supports multisig transactions for high-value buyer-seller interactions. In a multisig arrangement, cryptographic keys held by the buyer, seller, and marketplace must co-sign to release funds. This provides a mathematically protected escrow layer that cannot be bypassed even if one party acts in bad faith. For most standard orders, traditional escrow administered by trusted marketplace moderators provides sufficient protection. Sellers benefit from the system's structure: a protected dispute resolution process means legitimate vendors with good track records rarely face unfair chargebacks.
Marketplace Security at a Glance
- Anonymous registration — no email, no real identity required
- Hidden service (.onion) on Tor — seller and buyer IPs never exposed
- Multisig escrow available for cryptographically protected high-value trades
- Trusted, legitimate vendor program with community-enforced standards
- Anti-phishing phrase protects buyers from credential-stealing clones
- PGP encryption for all sensitive seller-to-buyer communications
- Bilingual EN/FR — authentic Canadian marketplace for all Canadian users
For a full breakdown of platform features, return to the WeTheNorth onion access home page which covers the complete security model, cryptocurrency setup, and Canada-only vendor community in detail.
WeTheNorth Market Guide — FAQ
hn2pawgbh5owvqgegyl5e445otpgntx64meszbo5e2o6nfk7szxknmyd.onion.
Always copy this URL directly from official WTN sources:
onion.wethenorthdnm.world,
mirrors.wethenorthdnm.world,
or wethenorthdnm.world.
Never use links from Telegram, Reddit, or any unverified source.
Verify the URL character-by-character before entering any credentials.
Access WeTheNorth Market Now
You have everything needed to access WeTheNorth Market securely. Use the verified onion address, enable PGP 2FA, set your anti-phishing phrase, and enjoy Canada's #1 darknet marketplace with mandatory escrow and bilingual EN/FR support.
Review the WeTheNorth security features or check the official onion mirror list on the home page. For cryptocurrency setup details, visit the BTC & XMR guide section.